Security
Leveraging data management and AI to rethink integrated risk management

Leveraging data management and AI to rethink integrated risk management

As enterprises move ahead with their strategic efforts at digital transformation, they also find that their approach to security must also transform. The new technologies of today’s dynamic digital world, such as cloud computing, IOT, and the interconnected supply chain, bring a raft of new challenges. Securing huge amounts of proprietary information and other critical business assets becomes exponentially more difficult, and meeting regulatory requirements more complex. Our three broad categories of security services help organizations drive productivity, business growth, and cost-optimization while establishing effective controls around sensitive assets.
Automation increases response times and overall security profiles
Unified security for cloud, multi-cloud, on-prem, and hybrid
Ensure your agile development efforts are secure by design
Change is constant in cybersecurity — continual, rapid, dynamic change. It’s impossible to maintain an effective defensive posture without constantly evolution. Security measures that worked in the past will not be effective today, and today’s security controls will not be effective tomorrow.
Many factors contribute to this rapid pace of change. Attacks are on the rise, and they are getting more advanced, persistent and stealthy each day, with some attackers even leveraging artificial intelligence (AI) to power their campaigns. Trends such as hybrid multicloud deployments, the internet of things (IoT), and mobile devices and services are making the attack surface larger and more complex. Traditional defenses are quickly outdated and the cybersecurity playing field has become a game of cat-and-mouse.
As cyberattacks grow in volume and complexity, artificial intelligence (AI) is helping under-resourced security operations analysts stay ahead of threats. Curating threat intelligence from millions of research papers, sensors, security devices, best practice guides that have been integrated, AI provides instant insights to help you fight through the noise of thousands of daily alerts, drastically reducing response times.Through machine learning and deep learning techniques, the AI improves its knowledge to “understand” cybersecurity threats and cyber risk.
AI gathers insights and uses reasoning to identify the relationships between threats, such as malicious files, suspicious IP addresses or insiders. This analysis takes seconds or minutes, allowing security analysts to respond to threats up to 60 times faster.
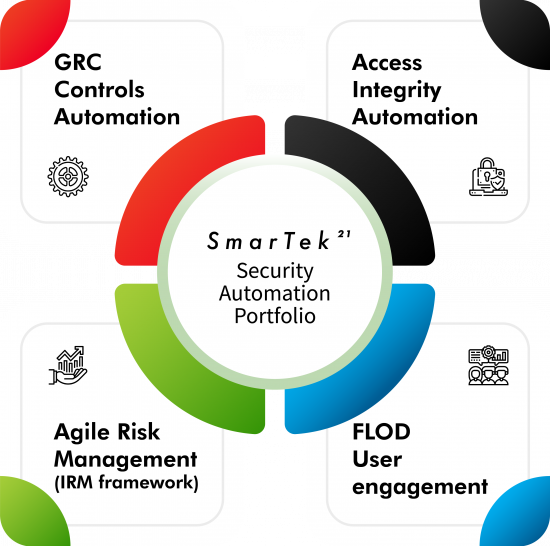

Automating GRC services can help in effective monitoring of risk and compliance processes, intelligent use of technology and data while improving time to value. These services can foster tangible value across IT operations through efficient use of resources, enhancing agility, and strengthening governance.
Agile security management is the continuous, pervasive and proactive method of protecting asset. There is an emphasis on involving everyone in the organization to help identity and report security and risk challenges, and to reduce dwell times through rapid response and automated analysis.


Agile security management is the continuous, pervasive and proactive method of protecting asset. There is an emphasis on involving everyone in the organization to help identity and report security and risk challenges, and to reduce dwell times through rapid response and automated analysis.
Security automation is the machine-based execution of security actions with the power to programmatically detect, investigate and remediate cyberthreats with or without human intervention by identifying incoming threats, triaging and prioritizing alerts as they emerge, then responding to them in a timely fashion.


SmarTek21’s compliance services not only identify data locations and types in the purview of GDPR, but also validates accuracy and generates a confidence/reliability score based on which stakeholders can take appropriate action.
This function enables data controllers to establish a repeatable action that can quickly scan large amounts of personal data throughout the data lifecycle. This is important, because GDPR compliance is an ongoing commitment, not a “once-in-a-year” task
The solution is designed around three key processes in the data supply chain—capture, curate and consume—and it does all the heavy lifting, from identifying how the data enters the enterprise system from structured and unstructured sources to which enterprise systems and processes use it, and for what purpose.
GDPR compliance is ultimately about protecting personal data and individual rights and freedoms. Organizations that see compliance as an opportunity to align their priorities to the principles of data ethics embedded in GDPR are poised to build a more secure and trustworthy foundation for sustained growth.
Avoid pitfalls of inaccurate data by assessing for quality, risk, and relevance—producing a veracity score to quantify trust within enterprise data.
Maximize value from your data with our multi-domain MDM, MDM for big data and MDM on cloud offerings.
Optimize, protect, and leverage data as a corporate asset across the data lifecycle.
Make your data more searchable and accessible—to use it to make business decisions and derive maximum value from it.
Complying with international regulations is the basis of ethical operations. Automate the compliance process with our machine-led compliance offering.

SmarTek21’s security services helps organizations prepare, protect, detect, respond and recover along all points of the security lifecycle.
Cybersecurity challenges are different for every business in every industry. Leveraging our global resources and advanced technologies, we create integrated, turnkey solutions tailored to your needs across your entire value chain.
Whether we’re defending against known cyberattacks, detecting and responding to the unknown, or running an entire security operations center, we will help you build cyber resilience to grow with confidence.
Collaboration lies at the heart of our approach to unlocking the business value of the cloud while addressing complex cloud security concerns. We work closely with our clients to identify a holistic set of security process and technology solutions that underpin cloud strategy, satisfy industry and regulatory requirements and achieve business goals. Among the benefits our collaborative approach to security providers are:
Collaboration lies at the heart of our approach to unlocking the business value of the cloud while addressing complex cloud security concerns. We work closely with our clients to identify a holistic set of security process and technology solutions that underpin cloud strategy, satisfy industry and regulatory requirements and achieve business goals. Among the benefits our collaborative approach to security providers are:
We help clients assess their security and risk tolerance, determine the right level of security for their cloud ambitions and design a comprehensive strategy and architecture to support their goals.
We implement processes and tools that centralize and streamline access to cloud and enterprise services and applications.
Security strategy and risk services
Maximize value from your data with our multi-domain MDM, MDM for big data and MDM on cloud offerings.
SecDevOps (also known as DevSecOps and DevOpsSec) is the process of integrating secure development best practices and methodologies into development and deployment processes which DevOps makes possible.
SecDevOps is a set of best practices designed to help organizations implant secure coding deep in the heart of their DevOps development and deployment processes. …It seeks to embed security inside the development process as deeply as DevOps has done with operations.
We need to ensure that we don’t consider security as an afterthought and that, across an entire organization, the benefits of implementing a security mindset — as well as the consequences of not doing so — are well understood.
A fundamental shift underway is the movement from “bolted on” security to “baked in” security, from adding security after production to building in security from the earliest point of development.
defines the set of DevOps tools used to setup and update infrastructure components. Examples include Ansible, Chef, and Puppet. …With IaC, if a system has a problem, it is disintegrated, and a new one (or two) are created to fill the spot.
The key to successful DevOps security lies in changing the underlying DevOps culture to embrace security—with no exceptions. As with any other methodology, security must be built into DevOps, To implement SecDevOps we need to revisit our existing DevOps pipelines, processes, and culture and ensure that security is integrated just as deeply and tightly as any other development consideration.
